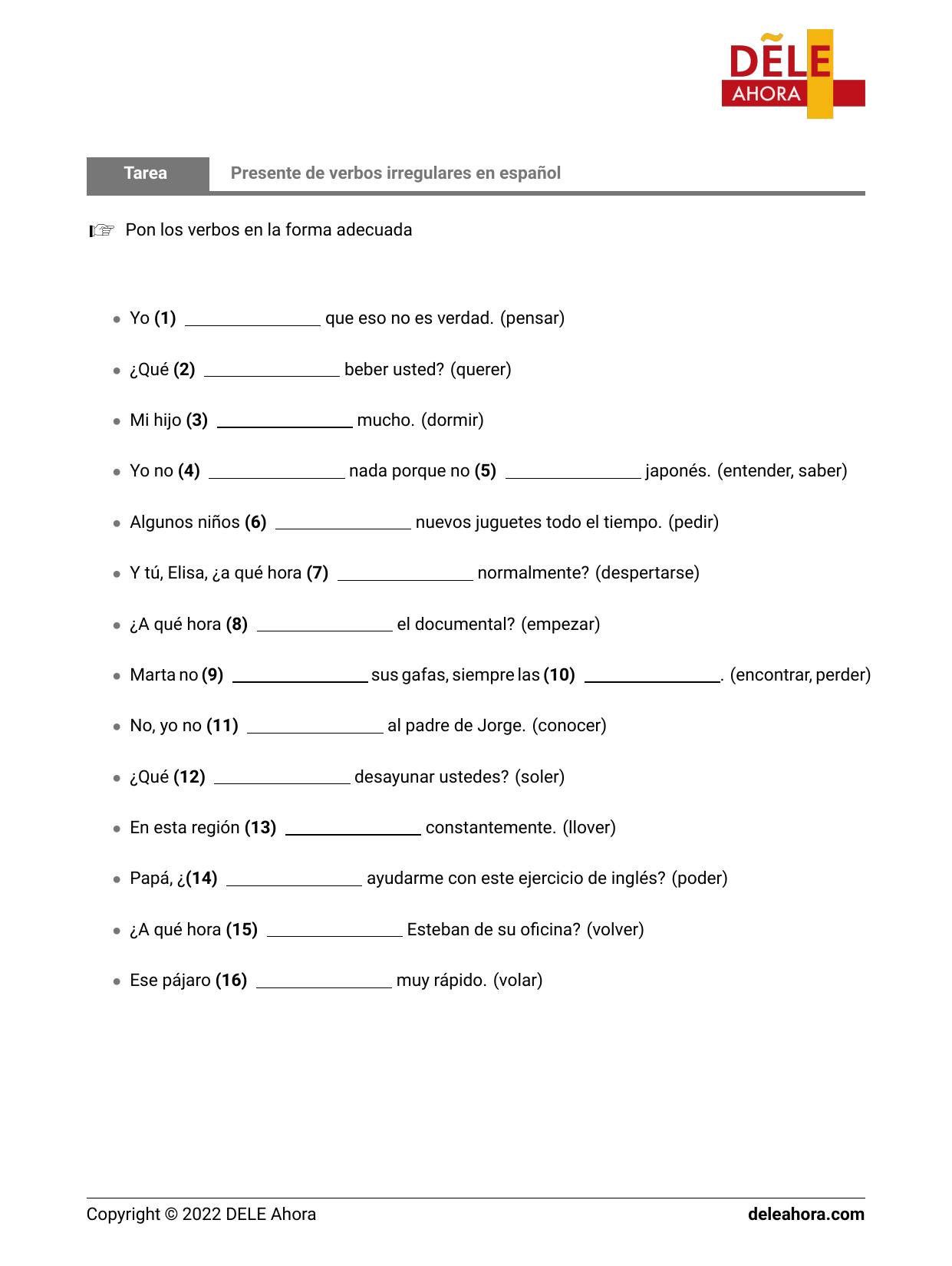
Presente de verbos irregulares en español Gramática
Presente de Indicativo - Verbos irregulares. Ejercicios interactivos para practicar el presente de indicativo en español de los verbos irregulares. Índice de contenidos. Presente: regulares Presente: irregulares 1 Presente: irregulares …